How China Built Iran's Surveillance State — and America Broke It
The Failures of China’s Surveillance Architecture in Iran
Winston kept his back turned to the telescreen. It was safer, though, as he well knew, even a back can be revealing.
- George Orwell, 1984.
An Old Problem
The internet was supposed to make repression in the 21st century expensive. The problem of control, however, is older than any technology built to exercise it. Jeremy Bentham had designed the original solution two centuries earlier, describing in 1791 a circular prison whose genius resided in uncertainty, a central tower from which guards could observe every cell while remaining invisible to the inmates, producing what Bentham called the sentiment of a sort of "invisible omnipresence."
Michel Foucault ( also a big fan at the time of the IR revolution), writing about the panopticon in 1975, identified precisely what made that architecture so durable as a theory of power — it induced in the inmate a state of conscious and permanent visibility that assures the automatic functioning of power, so that the prisoner, never certain whether he was being watched, began to police himself, internalizing the warden's gaze until the warden no longer needed to be present for control to function.
The internet kind of distorted that type asymmetry, as it is simply giving the prisoner the capacity to watch the warden, document the violence, and broadcast the footage to millions. For a decade it looked as though digital communication would make authoritarian rule structurally unsustainable, and repressive governments from Moscow to Tehran spent the early 2000s treating connectivity as an existential threat manageable only by slowing its spread.
Then the surveillance industry answered the problem.
The panopticon could be rebuilt at national scale with Chinese components, sold under the administrative language of smart-city modernization, and embedded so deeply into telecommunications infrastructure that no citizen documentation could escape it. Nowhere did that reconstruction go further than in Iran, where the Islamic Revolutionary Guard Corps and the People's Republic of China spent 15 years assembling a machine of invisible coercion that only the combined force of American satellite technology and strikes finally broke open.
The IRGC Plugs In
The Islamic Republic arrived in 1979 with a fully formed appetite for silencing, and for two decades the familiar instruments held the line well enough. The Ministry of Culture and Islamic Guidance licensed all publications and conditioned access to print on editorial compliance, while the Press Court prosecuted editors and journalists under laws written broadly enough to imprison anyone whose reporting the judiciary chose to call a threat to national security.
The reformist press that briefly flourished under President Khatami disappeared under a coordinated judicial campaign beginning in 2000, when dozens of newspapers shut within weeks and their editors went to prison, a demonstration that the clerical establishment enforced its ceilings on liberalization by force. What those instruments could not survive, however, was the arrival of mass digital connectivity, which ultimately confronted the regime with a challenge that licensing and prosecution were architecturally unsuited to resolve.
In fact, the Green Movement of 2009, the mass protests following the disputed re-election of Mahmoud Ahmadinejad, showed what open connectivity meant for a government whose authority rested entirely on controlling the flow of information. Protesters coordinated through mobile networks and social media with a range and velocity that overwhelmed the security services' capacity for pre-emptive disruption, and the episode forced a fundamental institutional reassessment inside the Revolutionary Guard whose conclusion was unambiguous — connectivity was a security variable requiring direct command, and any institution intending to maintain authority over Iranian society would need to own the infrastructure through which that society communicated.
The IRGC translated that conclusion into institutional structure without delay, acquiring a majority stake in Iran's state telecommunications company through an IRGC-linked consortium and transforming the nation's largest mobile carrier into a vehicle for political administration.
The IRGC Cyber Army, emerging from the same period, extended the organization's informational reach beyond Iran's borders through harassment campaigns against journalists and opposition figures operating abroad, while the National Information Network expressed the regime's longer ambition — to replace the global internet entirely with a closed sovereign system the IRGC could administer from the center.
By the time Chinese surveillance technology arrived at scale, the Revolutionary Guard had already spent a decade building the two institutional pillars that made absorption possible.
The first was ownership of the physical network through which Iranians communicated.
The second was a parallel intelligence apparatus penetrating every workplace, university, and association or society in the country, generating a granular map of Iranian civil society as a permanent institutional output.
Together those two pillars produced an organization that knew where dissent lived and controlled the wire through which dissent moved. Beijing supplied the technology to act on both at speed, and the two organizations recognized in each other something closer to a shared doctrine.
What Beijing Delivered, and How Tehran Used It
China treats control of information as the foundational precondition of political order, and the surveillance architecture Beijing developed reflects a coherent theory of governance built around a conviction Xi Jinping stated without ambiguity in internal documents later published by state media.
"Anti-China forces in the West have always tried to topple China via the internet," Xi explained. "Whether we can hold on and win the fight on the battlefield of the internet matters to our ideological security and regime safety."
The surveillance institutional machinery Xi promoted assembled to fight that battle operates through three main interlocking layers:
The Great Firewall eliminates the informational commons through which political opposition organizes, severing the connective tissue between dissidents before they achieve any collective political form.
A behavioral compliance architecture conditions citizens through anticipatory consequences, training populations to self-censor before enforcement action occurs and making the internalization of conformity the primary mechanism of discipline.
Predictive policing algorithms then aggregate data from facial-recognition feeds, mobile device tracking, financial transactions, and travel records to generate individual risk scores that trigger detention before any act of dissent takes place, giving the state the capacity to suppress opposition that has not yet expressed itself.
The Revolutionary Guard recognized in China's model a structural affinity with its own organizational doctrine for two reasons that had nothing to do with ideology. Indeed, both organizations had concluded that political control required owning the infrastructure of communication rather than merely policing its content, and both had built parallel intelligence networks designed to suppress collective action before it achieved any organized form. The IRGC moved very quickly to acquire the technology required to replicate what Beijing had built at scale.
In 2010, ZTE signed a $130 million contract to overlay a comprehensive surveillance system onto Iran’s state-managed telephone and internet networks, while Huawei established itself concurrently as the country’s largest telecommunications equipment provider, supplying location-tracking services to mobile carriers and presenting Iranian officials with content-censorship tools modeled on systems already deployed inside China.
The deep packet inspection technology these firms supplied allowed security services to monitor encrypted communications in real time, identify the geographic clustering of dissent, and throttle connectivity in targeted areas without any visible indication that an intervention had occurred, giving the IRGC a degree of operational invisibility that no previous instrument of censorship had approached.
By early 2026, a Huawei-supplied internet kill switch project estimated between $700 million and $1 billion neared completion at a fortified data center outside Tehran, engineered to give the IRGC the capacity to sever Iran’s global connectivity.
Above that foundational layer, Tiandy Technologies built the system and structure of street-level suppression, delivering systems designed to flag behavioral anomalies in public spaces, and video-analysis platforms capable of mapping protest networks.
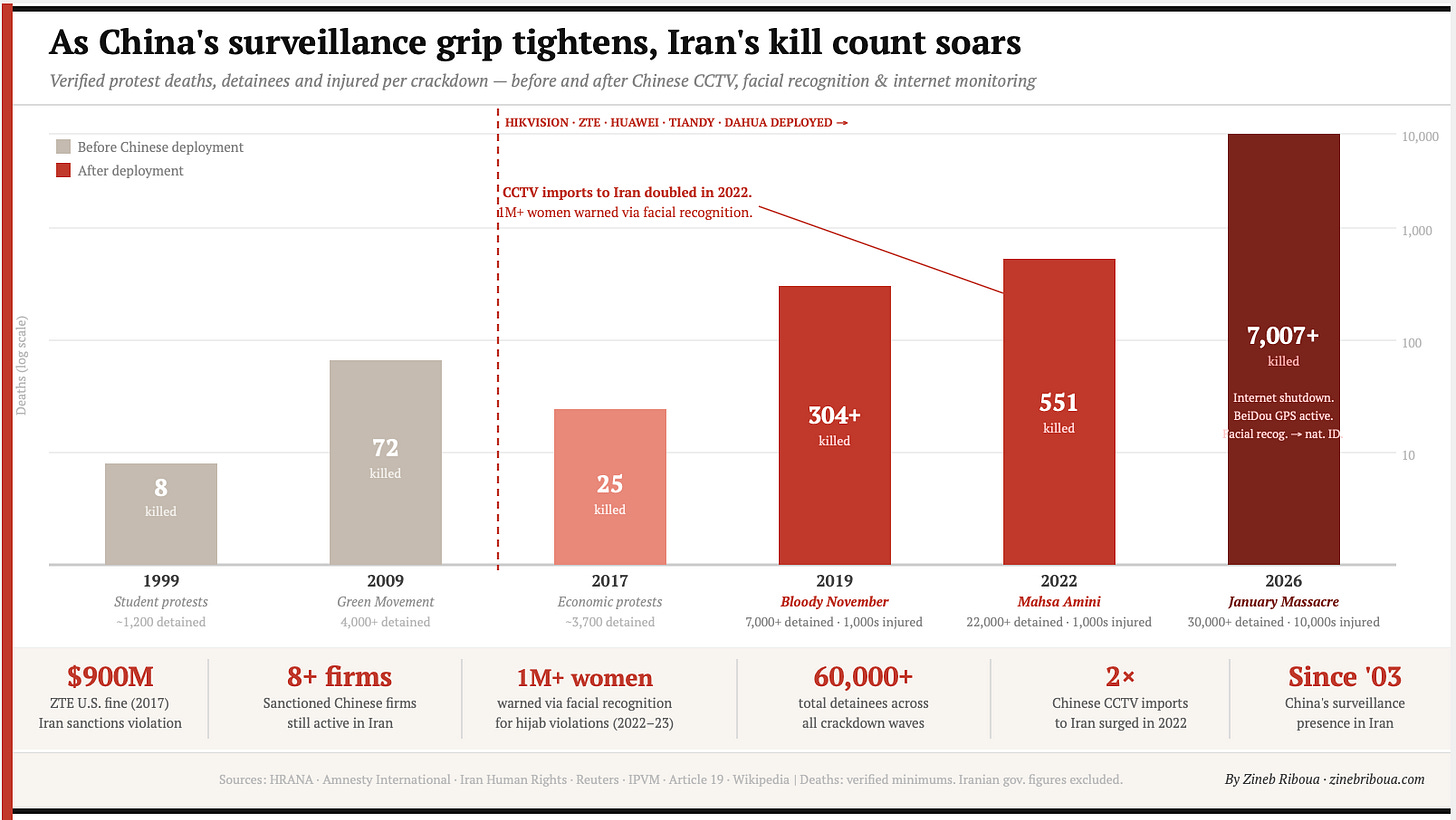
After the 2022 protests that followed the death of Mahsa Amini, Iranian officials deployed these technologies as a substitute for the morality police, whose physical visibility had rendered repression politically costly and had accelerated the very mobilization the regime sought to prevent, replacing officers on the street with cameras that identified women without headscarves, issued automated warnings, and triggered arrests without any human presence at the scene.
Iran’s police chief announced in 2023 that “the era of the street patrol is over; we will use technology and cameras” for hijab enforcement.
The operational cement holding this architecture together hardened most visibly in agreements Iranian officials signed in public and defended without embarrassment. In 2024, Iranian Police Chief Ahmad-Reza Radan, sanctioned by the European Union for directing lethal repression, traveled to Beijing and signed a memorandum on law enforcement cooperation with China's minister of public security, committing to upgrade security collaboration under the stated category of counterterrorism.
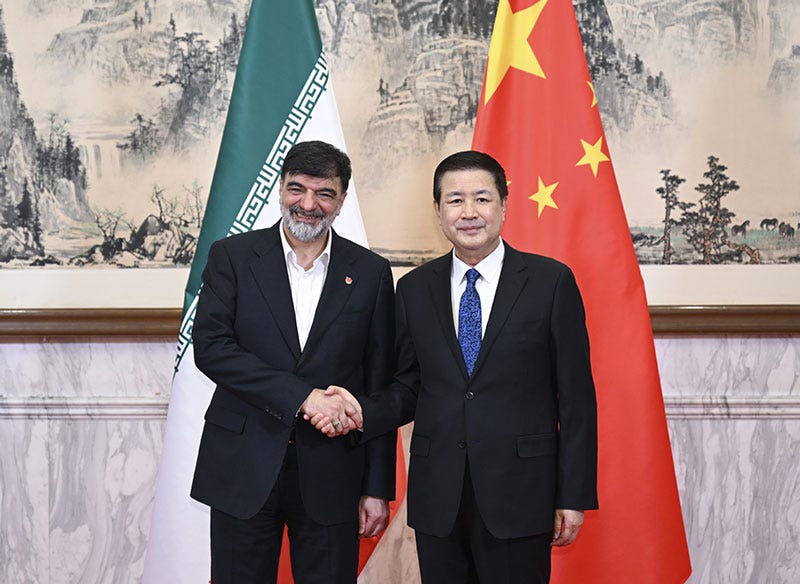
In December 2025, just days before the uprising that would shake the regime, Iran’s ambassador to China visited the People’s Public Security University and pledged continued practical cooperation in law enforcement and security.
It has also been documented that China’s police training programs for Iranian security personnel served simultaneously as vehicles for exporting Beijing’s stability-maintenance doctrine and as commercial opportunities for Chinese surveillance firms, ensuring that ideological transmission and market expansion advanced through a single institutional channel and that every training cohort returned to Tehran carrying both a political framework and a procurement relationship.

The Day China’s Surveillance Architecture Failed
The January 2026 uprising tested everything the IRGC and Beijing had assembled together, and for a time the machine performed as designed. Authorities severed internet and telephone access as protests spread from Tehran to Ilam, deploying the internet shutdown capability that Chinese firms had spent years engineering for precisely this contingency, while monitoring tools identified organizers, mapped social networks, and enabled mass arrests before demonstrations could consolidate into movements with the organizational depth required to sustain pressure on the government.
With visibility suppressed and outside documentation made impossible, security forces fired into crowds, raided hospitals, and detained the wounded in circumstances the regime had spent a decade and billions of dollars ensuring the world could not observe in real time, and medical networks inside Iran estimate that as many as 16,500 protesters were killed and over 300,000 injured under that information blackout.
What essentially broke it was satellite connectivity the regime could not reach.
In fact, the State Department smuggled roughly 6,000 Starlink terminals into Iranian territory in January 2026, and President Trump, who had according to media reports discussed the operation directly with Elon Musk, wrote publicly that help was on the way, turning a covert infrastructure operation into a political message directed at both the protesters and the regime.
Iranian security forces responded with Chinese and Russian jammers and conducted house-to-house searches in neighborhoods where satellite signals had been detected, but the footage had already escaped, and once footage of hospital raids and crowd shootings cleared the sealed information environment, the political cost of the violence rose sharply enough that the regime found itself performing publicly the repression it had spent years learning to render invisible.
The Starlink operation exposed three important failures in the ultra-surveillance architecture that no technical patch or Chinese software can address.
The Chinese model of control requires an actual physical monopoly over connectivity, and satellite infrastructure, but the kind Washington smuggled into Iran operates outside the layer of the network the state owns, making suppression contingent on jamming equipment that cannot be deployed at national scale without disrupting the same communications the regime depends on to coordinate its own security forces.
The second failure is operational. Data collected without the command capacity to act on it isn’t really intelligence, it’s just a giant inventory, and the Iranian state that emerged from the 12-day war is a state whose decision-making ecosystem can no longer close the distance between what its surveillance apparatus sees and what its security forces do with what they see. It’s a subtle difference, but an important one.
The third failure is behavioral and strikes at the foundation on which the entire model rests. The system's power derives not from catching every act of dissent but from persuading the population that every act of dissent will be caught, and that persuasion holds only as long as the architecture appears impenetrable. Once tens of thousands of Iranians acquired Starlink terminals, used them openly, and suffered no immediate consequence, the belief in the system's omnipresence as the mechanism of control just completely dissolved, and no quantity of cameras or intercept infrastructure can reconstruct it in a population that has already discovered the gaps. The taboo has been broken.
Why It Matters
It’s worth noting that Chinese firms supply surveillance infrastructure in at least 150 countries, from camera networks in Vietnam to citywide monitoring systems in Kenya, even in Gulf countries, and the failure of that architecture to stabilize the Iranian state under military and informational pressure sends a signal to every government that purchased the same system and the same promise of durable control.
Operation Epic Fury is still underway, and what is happening inside Iran’s information environment at this moment remains largely unknown. What is known is that the operation has targeted the command nodes responsible for activating the connectivity shutdown and the personnel with the administrative authority to order a national blackout, meaning that the technical capacity to seal the information environment may no longer exist in a form the regime can operationalize.
That outcome matters beyond Iran because the connectivity/internet shutdown was the single capability that made every other component of the Chinese surveillance architecture function as designed, built on the assumption that the regime could, at the moment of maximum threat, reduce the information environment to what it controlled and nothing more. But with General License D-2 it positions American companies to move into that opening at commercial speed, and the Starlink terminals already distributed across Iranian territory mean that the population most likely to protest in the weeks ahead is also the population best positioned to document what happens when it does.
Beijing has long argued that the sophistication of its domestic surveillance architecture makes it immune to the class of pressure the United States can apply, a claim the Iranian case has now tested against operational reality. That promise was always a theory. Iran was the proof case, the proof case has now failed, and it was America that broke it.



Canada is trying to erect just such a system through proposed legislation. If the liberal government gets a majority there won’t be a lot we can do to stop it. I have often wondered if starlink would be helpful to have in terms of freedom. This article is very helpful and hopeful.
This is a great article. So much of hard work and extensive research.
As for Iran, Chinese companies often accuse Iranians of buying the first batch of technology and then copy with reverse engineering. In fact they sound reluctant to supply Iran with the top of the art technology. In one instance, I heard that Iran had produced and sold surveillance equipment to other countries.